Given the sheer quantity of information we store on our phones, hackers are constantly coming up with new ways to access our private information. SIM hacking, swapping and cloning is the latest in this line of attacks on our privacy.
If you’re wondering how to tell if your SIM card has been hacked, cloned or even swapped, then this article is for you. I’ll cover some of the signs that can indicate your SIM card has been compromised and what steps to take next.
I’ll explain what all these things mean, how they are done and what you can do to protect your SIM card.
If you suspect that someone might have hacked your SIM card then there are a few things you can do right away to protect yourself against further damage or loss of money.
Let’s get to it now.

Why Do People Hack SIM Cards?
You’re probably wondering why hackers want access to your SIM card anyway – it doesn’t have a lot of information on it. While it doesn’t have a large quantity of data on it, a SIM card can still be used to gain access to other data on your phone. Here’s how:
Banking Fraud
If you’ve ever made a transaction online, you must be familiar with two-factor authentication. You receive a one-time password (OTP) via text to authenticate online transactions. Hackers can gain access to OTPs via your SIM card.
Since the monumental rise of Bitcoin, cryptocurrency investors are also a hot target for SIM card hackers.
Impersonation
By hacking or cloning your SIM card, hackers gain access to your calls and text messages. They can also make calls or send texts posing as you. This basically means that they could impersonate you if they wished to.
They could gain access to your bank accounts or social media or access the data of your close ones by pretending to be you.
Accessing Private Data
For various reasons, people often choose to spy on other people’s conversations and private data to gain information about their life.
Leaking private conversations or pictures on social media is also a common phenomenon, especially if you are a high-profile individual.
Social Media Accounts
Social media celebrities are on the rise and so is the demand for their account details on the black market. Since social media logins require two-factor authentication, hackers target the SIM card of popular influencers to hack into their accounts.
Methods of Hacking a SIM Card
Fortunately, there aren’t that many ways to hack a SIM card. Hackers usually use one of the following:
Sim Swapping
SIM card swapping is a method of hacking where the hacker contacts your phone service provider and convinces them to swap your number to a new SIM. They do this by gathering data from your social media and executing phishing scams first.
Sometimes staff members run ‘SIM Jacking Rings’. Hackers contact a staff member at a service provider company who then swaps SIM cards in bulk for them.
The final step to successfully swap a SIM card is to restart the phone. This is achieved by impersonating the service provider and sending a fake message asking the user to restart the phone.
As a side note your service provider will never randomly phone you or text you to restart your device. They just don’t do this!
Sim Card Cloning
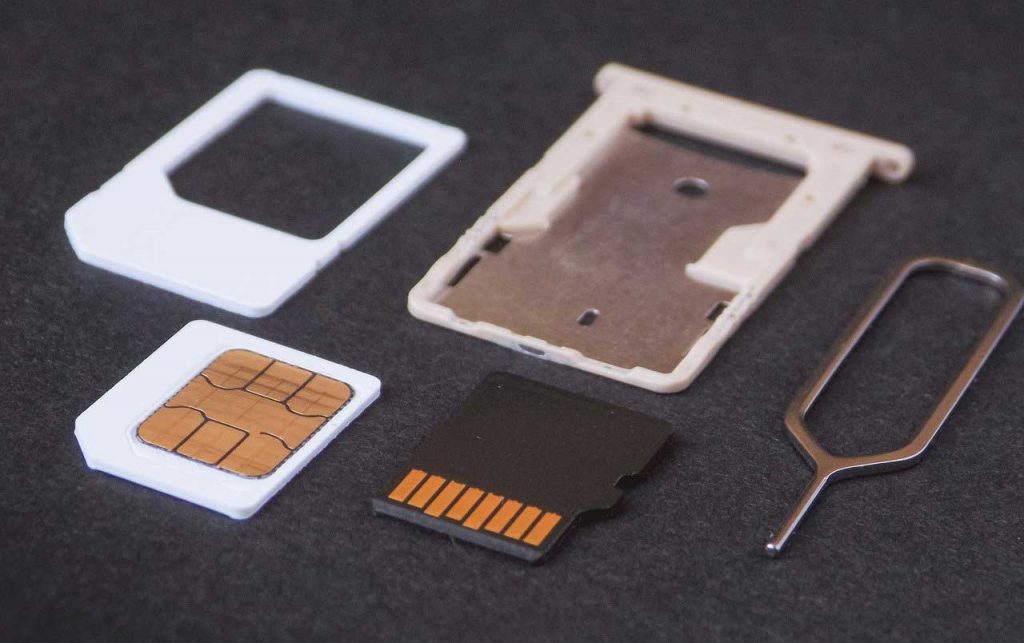
SIM cloning requires physical access to your SIM card. Once a hacker gets a hold of your SIM card, they place it in a card reader and attach it to their computer. They then use a SIM writer to copy your SIM card information to a new one.
SIM writers have many legal uses and are thus easily available online. You can purchase a SIM writer online for about $10-$15.
Once a hacker clones your SIM, he can access your calls, texts and location data and make calls or texts pretending to be you.
Thankfully these types of SIM hacking are quite rare. They involve technical expertise and can be hit and miss in their success. However the most common threat from phone hacking you’ll come across will be by phone spy apps.
See my main guide covering phone hacking methods for more details. These apps don’t hack the SIM card – but the actual phone!
How to Know if My SIM Card Has Been Hacked?
I get this question a lot. If your SIM card has been hacked, cloned or swapped, you will notice some or all of the following signs:
- Radio Silence: If you stop receiving calls and messages, it is a surefire sign that your SIM card has been hacked. You can test this by asking someone to send you a text or call you. If you do receive it, your SIM card is safe.
- Request to Re-Start your phone: If a hacker has swapped your SIM, he cannot activate it without restarting your device. If you receive a message asking you to restart your phone, you might be the victim of SIM swapping.
- Incorrect Location History: Go to services like ‘Find my device’ or ‘Locate my device’. If you see a different location than the one you’re in, your SIM has probably been hacked.
However, hackers could potentially disable this location, so look out for other signs as well.
Access Denied: Once they have access to your SIM cards, hackers can get past the two-factor authentication that most banking systems, shopping sites and social media use.
If you cannot access your social media, bank accounts or your Amazon account, your SIM may have been hacked.
Stranger Danger: Always read through the activity listed on your phone bill. If there are calls to unfamiliar numbers or any activity that you didn’t do, it’s time to have a chat with your service provider.
How to Prevent SIM Hacking, Swapping or Cloning
Now that you know about identifying SIM swapping and cloning, let’s talk about preventing it.
Look Before You Click
Do not click on any links unless you are 100% sure of their origin. Do not open any links you receive on email or text they could be phishing attacks. This is how hackers gain access to your data for SIM swapping.
Do not install any unnecessary apps. Hackers often lure people by promising rewards or discount codes. These apps could contain cloning software or other malware. Always remember, there’s no such thing as a free lunch.
Avoid Oversharing
Avoid sharing too much personal information online. There are new kinds of hacks coming to light every day. The more accessible you are, the more vulnerable you get.
SIM swapping requires hackers to obtain personal information about you in order to impersonate you. There is no point in making their job easy by serving up every detail of your life to them online.
Put a PIN in It
Most cellular networks now give you the option to set up a password or PIN in addition to two-factor authentication.
Both Verizon and AT&T offer this service. Contact your service provider for more information on how to create a PIN or password for your account.
We know that nobody wants to remember yet another PIN or password. But adding this small step of security could save you a lot of hassle later.
Remove Your Number
Not every account needs your phone number. Remove your phone number wherever possible. Alternatively, you can set up a Google Voice Number, which is not susceptible to SIM card hacks.
Hackers can also use your phone number in so called Vishing scams – see that guide for what that means and how it works.
If you have a particular asset you want to protect, like cryptocurrencies, for example, keep a separate number for that account. Do not share this number with anyone.
They might seem like extreme measures but if you want to protect your hard-earned assets, you need to go the extra mile.
Keep Your MEID Number Safe
Your MEID number is linked to your SIM card and your IMEI number is linked to your phone itself. Hackers can use these numbers if they find them out so keep them safe.
Not sure what these numbers mean? See my guide MEID vs IMEI Numbers. Then check out how to check your IMEI number. You’ll be an expert after reading those guides!
Keep Your Phone Close
SIM cloning requires physical access to your SIM card. Protection against that is fairly easy so don’t leave your phone unattended.
Having said that, we cannot always ensure total protection. Your phone might get lost or stolen, which means your SIM card could end up anywhere – along with all your sensitive data.
If you have serious concerns about your cell phone security you should check out my Premium Security Guide. It covers all aspects of phone hacking and spy apps including how to find and remove the threats quickly and easily.
The guide is designed for people who are not technical experts but still want protection. Have a look below.
The Final Word
Technology evolves every day and so do hackers. The only way to protect yourself is to constantly stay vigilant of all your activity online.
SIM card hacking and cloning is possible but most people will not be targeted due to it’s complexity. It still pays to be aware of the threats.









